Crime & Crime Prevention
Crime and Crime Prevention is a challenge for every government and society. Learn more about how governments deal with crime, criminals and crime prevention.

Can Anyone Make a Citizen's Arrest?

Who Owns the Copyright, AI or the Artist?

What Does the ICC Putin Arrest Warrant Actually Mean?

Supreme Court on the Brink of Ending Affirmative Action in College Admissions

Are Skittles 'Unfit for Human Consumption'? A Lawsuit Says Yes

Do Unbiased Jurors Exist in the Age of Social Media?
Learn More
By now, it's probably a familiar sound: jarring, ear-splitting tones that sound from your mobile device. Known as an AMBER Alert, these emergency notifications can be pivotal in finding abducted children. Named after Amber Hagerman, the system started in 1996.
By Yara Simón
Gary Francis Poste made headlines after his death as the suspected Zodiac Killer. But is there enough evidence to finally close this case?
By Sascha Bos
In November 1984, at the age of 17, Lisa McVey Noland was riding her bike home from work in Tampa, Florida, when she was abducted by a serial killer.
By Sascha Bos
Advertisement
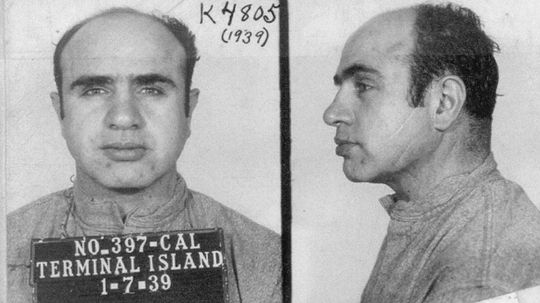
Dive into the world of La Cosa Nostra. Discover its origins, impact, and intriguing aspects of this infamous organized crime syndicate.
Explore the enigmatic Bonanno Crime Family. Discover its origins, criminal operations, and intriguing legacy in organized crime.
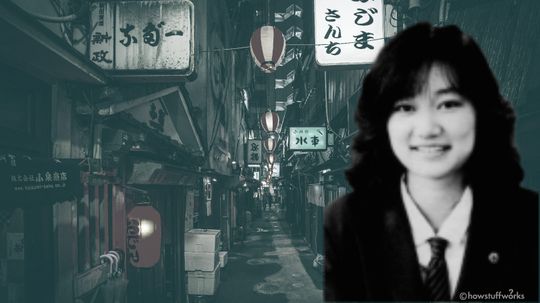
Junko Furuta was a Japanese schoolgirl, brutally raped and killed by four young men, who received shockingly light sentences. How did they get off so easily?
By Dave Roos
Because of the murkiness of maritime law, it's hard to pursue crimes committed on cruise ships. What makes it so easy to get away with a crime on the high seas?
By Julia Layton
Advertisement
Now that former President Donald Trump has been indicted by the Justice Department, what happens to his Secret Service detail? Would he get protection if he goes to prison, too?
By Dave Roos
Former President Donald Trump was arraigned but didn't have his mug shot taken. Why not, and what's the deal behind this police photograph?
The reproduction of books, movies and songs is closely protected by copyright law, but intellectual property in the public domain can be used by anyone for free.
A Netflix docuseries about serial killer Jeffrey Dahmer is one of its most-watched shows ever. We reviewed FBI files of his case instead and got a chilling look at what drove him to kill.
By Suzie Dundas
Advertisement
While the U.S. is in full support of investigating Vladimir Putin's war crimes in Ukraine, it's long opposed the International Criminal Court at The Hague. But why?
People have been raising alarms about the potential for nonconsensual, surreptitious collection and testing of DNA for years, but will genetic paparazzi with DNA collection kits become as ubiquitous as those with cameras?
H.R. 8, which passed the House last year, would eliminate private gun sale loopholes and require nearly universal background checks. But it faces difficult odds of passage in the Senate.
ADX Florence is the only federal "supermax" prison in the U.S. and home to a rogue's gallery of notorious criminals. What's it like to serve time there?
By Dave Roos
Advertisement
U.S. President Joe Biden accused Vladimir Putin of committing genocide in Ukraine. But who really determines whether a genocide is occurring, and how?
Arne Johnson stabbed a man to death in 1981. His intended legal defense? Guilty by reason of demonic possession. Did it work?
By John Donovan
A jury in Kenosha, Wisconsin, found Kyle Rittenhouse not guilty on all charges. A Harvard legal scholar weighs in on why the verdict directly challenges the legal standards for self-defense.
True crime is often stranger than fiction. How much do you know about some of the strangest and most notorious criminals out there like Ted Bundy, Jack the Ripper and the Night Stalker?
By Alia Hoyt
Advertisement
Indigenous women have been going missing and been murdered along an infamous stretch of highway in British Columbia since the 1960s. But not much is being done to find them — or who killed them.
By John Donovan
Cities like Chicago are spending millions for high-tech systems that can identify and pinpoint the exact location of a gunshot. But are these systems worth the price tag?
By John Donovan
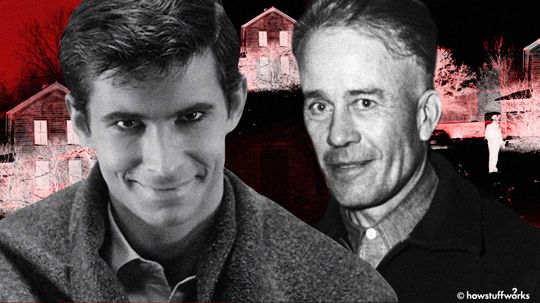
Ed Gein was known as the "The Butcher of Plainfield" for killing two women in the late 1950s. But he was also the inspiration for iconic horror movie characters, including Psycho's Norman Bates and Texas Chainsaw Massacre's Leatherface.
By John Donovan
The Netflix documentary "This Is a Robbery" attempts to solve the 1990 Isabella Stewart Gardner Museum heist. Today, the 13 stolen pieces of artwork are worth around $500 million. Have you seen any of them?
By John Donovan
Advertisement
Despite how hard investigators work, some crimes just baffle even the most gifted detectives. They go cold. That's where these nine cases stand. Will they ever be solved?
By John Donovan
One day they were here and the next they simply disappeared. What happened to these 14 people? Will we ever know what happened to them or will their fates be unsolved forever?
By John Donovan